Latest News for 4TC
We have loads to say!
We have loads to say!
The transformative power of Artificial Intelligence (AI) has already begun to reshape the job landscape, and according to the McKinsey report “The State of AI in 2023: Generative AI’s Breakout Year,” this trend is only set to accelerate. The report highlights key insights into the potential changes in the job market, emphasizing the need for adaptability and preparedness among workers and industries. In this article, we delve into these five crucial insights from the report, shedding light on the implications of Generative AI on the workforce.
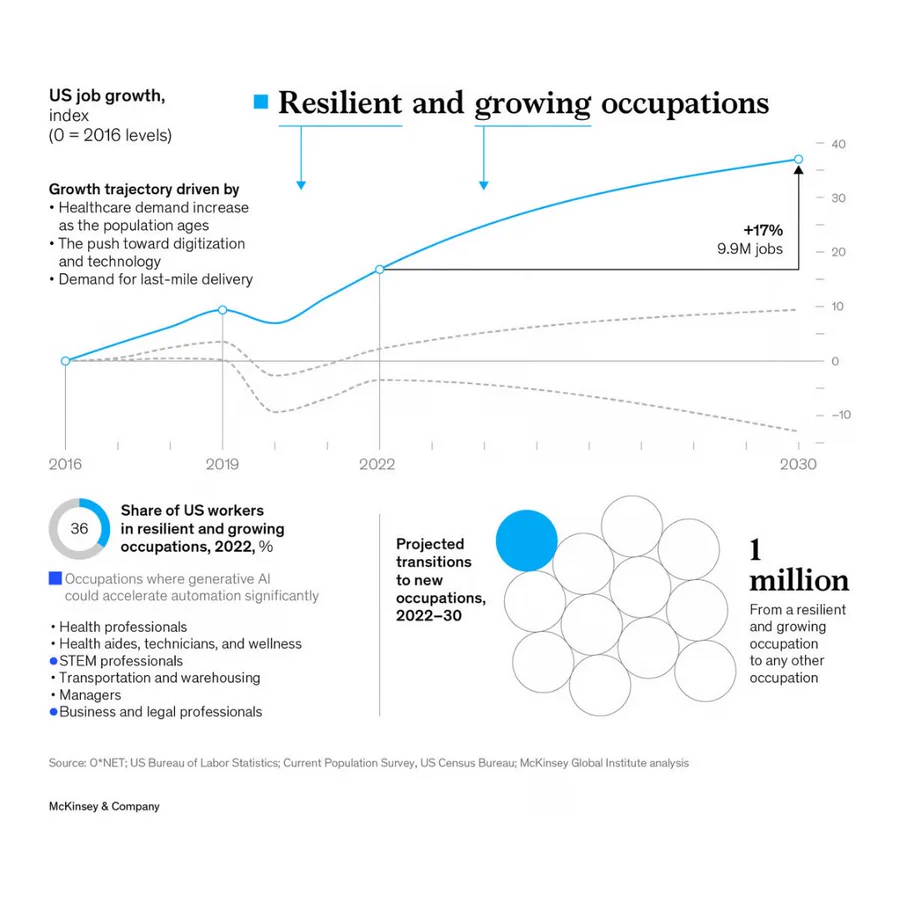
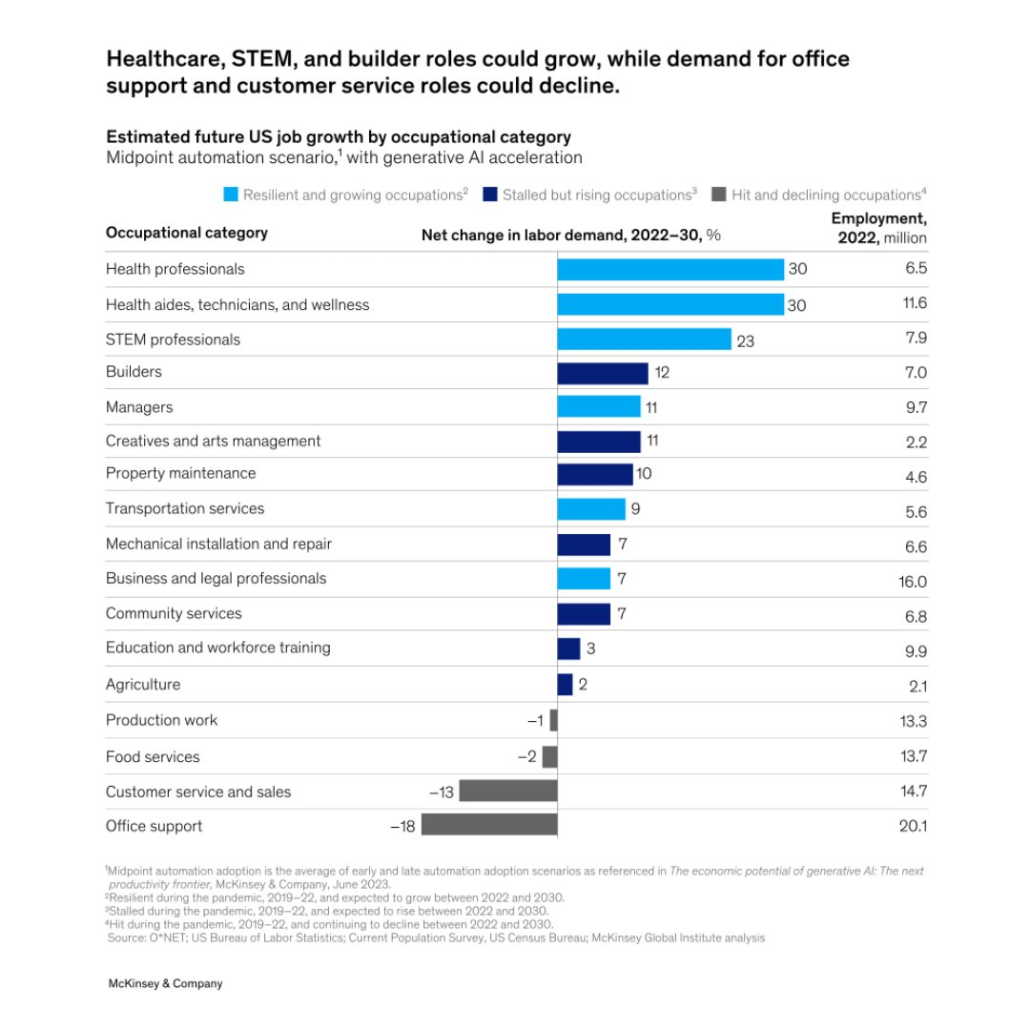
McKinsey’s report predicts that by 2030, approximately 12 million people in the US will need to transition into new job roles as Generative AI advances. Automation, driven by generative AI technology, is expected to replace many routine and repetitive tasks across various industries. While this may lead to enhanced productivity and efficiency, it also challenges the workforce to adapt and reskill.
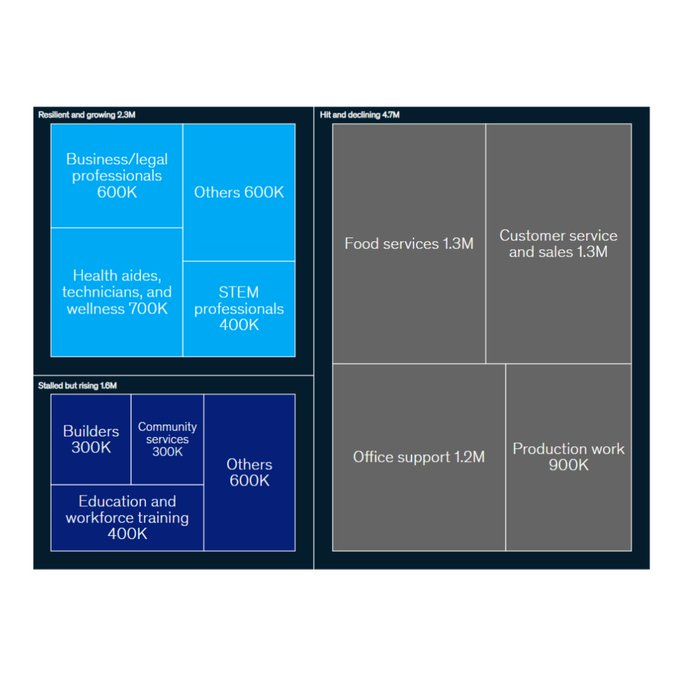
The report highlights a significant trend in recent job changes in the US. Over half of the 8.6 million job transitions observed were people moving away from roles in food service, customer service, office support, and production. These roles are particularly susceptible to automation as they often involve repetitive and predictable tasks that can be efficiently performed by AI systems. The workforce’s response to these shifts will determine the pace of transformation in the job market.
Generative AI’s capabilities are poised to disrupt the job market significantly. The report suggests that by 2030, up to 30% of jobs could be automated by this technology. This automation is likely to impact various sectors, including manufacturing, finance, and customer service, among others. However, it’s important to note that automation doesn’t necessarily mean job elimination; instead, it might entail the transformation of job roles and the creation of new opportunities.
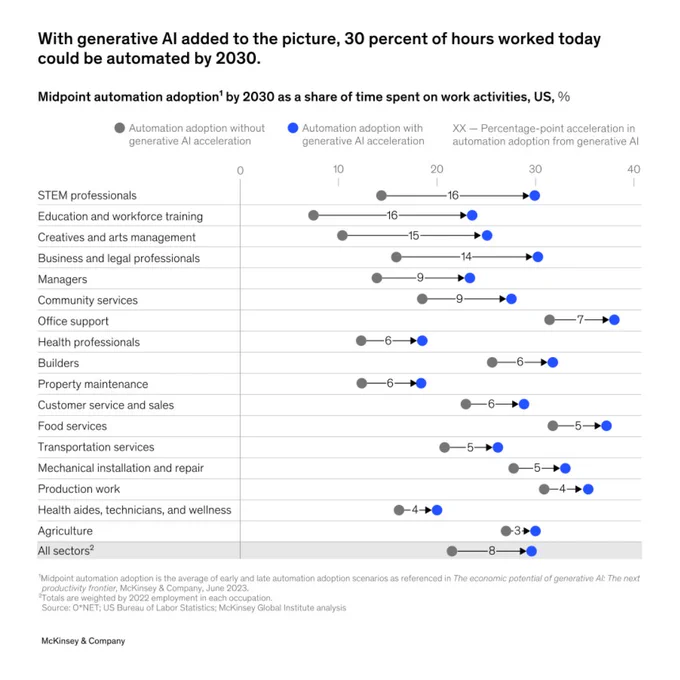
While Generative AI can automate many jobs in fields like Science, Technology, Engineering, Mathematics (STEM), healthcare, construction, and other professional domains, it also presents opportunities for growth in these industries. For instance, Generative AI can assist healthcare professionals in diagnostics and treatment planning, enhancing patient care. In construction, AI can optimize building designs and streamline project management, increasing efficiency.
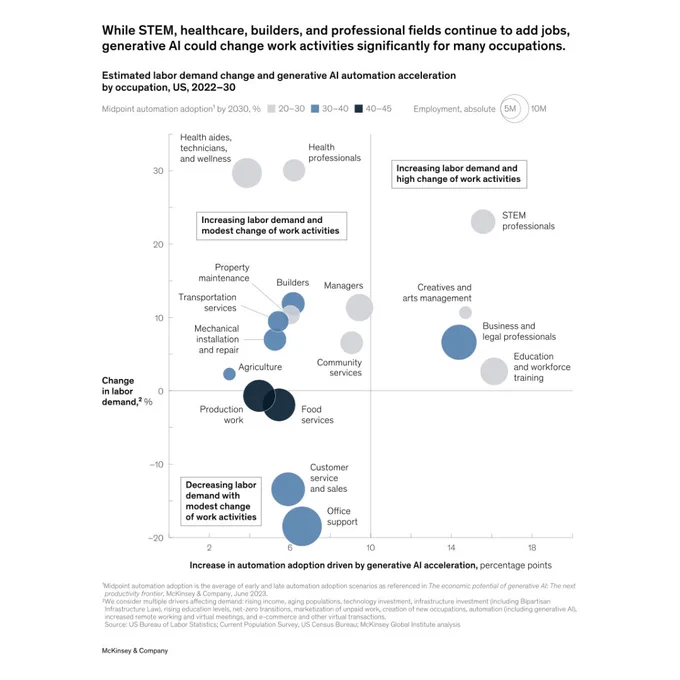
The McKinsey report highlights the differing growth trajectories across industries. Healthcare, STEM, and construction sectors are experiencing job growth, driven by technological advancements and an aging population’s increasing demand for healthcare services. However, the report also reveals that office support and customer service jobs are declining, largely due to automation and digitalization.
The McKinsey report paints a comprehensive picture of the potential impact of Generative AI on the job market by 2030. While automation presents challenges for certain sectors, it also offers transformative opportunities for growth and efficiency. The future of work will undoubtedly be shaped by the adaptability of the workforce and the ability of industries to leverage AI technologies responsibly.
As we embrace the AI-driven future, it becomes crucial for workers to reskill and upskill themselves, ensuring they stay relevant and agile in a dynamic job market. Additionally, businesses and policymakers must collaboratively devise strategies to support workers through these transitions, enabling them to seize new opportunities in an AI-powered world.
Check out the Full Report. All Credit For This Research Goes To the Researchers on This Project.
Microsoft yesterday released then quickly pulled an internal tool for enabling experimental Windows 11 features.
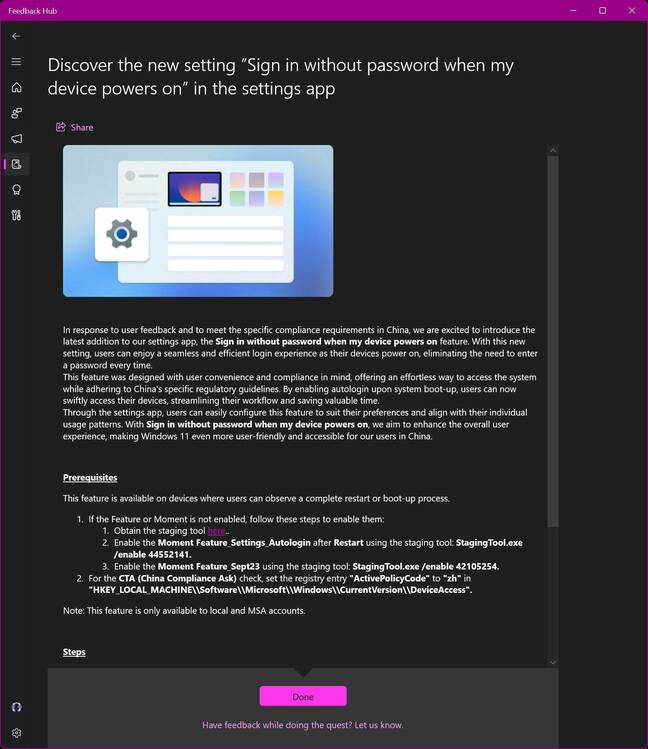
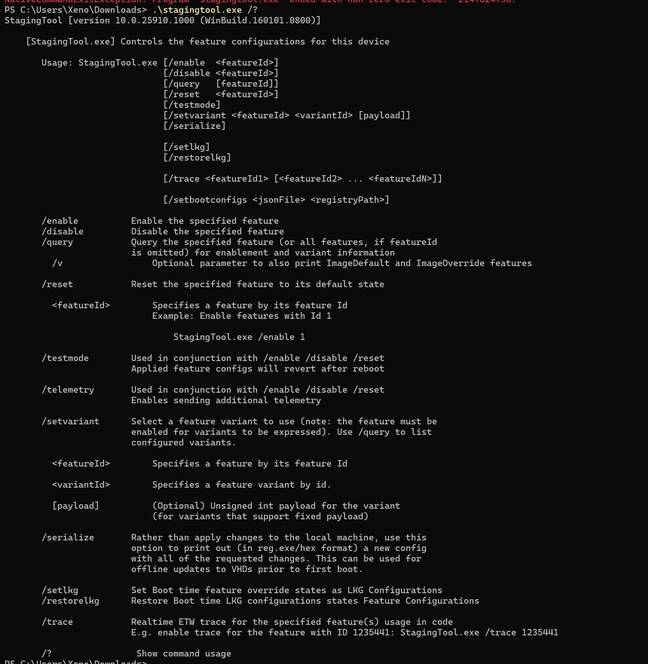
The StagingTool app was offered to Windows Insider fans in a Microsoft Bug Bash quest. These quests essentially invite users to try out specific features or functionality and see if they can hit a bug and report it, presumably so engineers can home in on the problem. This test program often precedes a major Windows release, such as the Windows 11 23H2 update that is scheduled to land sometime this autumn.
Indeed, on Wednesday, the IT giant kicked off another round of quests.
And as discovered by a netizen using the handle XenoPanther, a Windows Insider Canary participant, two of the latest Bug Bash quests included links to StagingTool and instructions to download the app and use it to enable certain features for testing.
So far so good. But then those links to StagingTool were torn down not long after XenoPanther’s discovery, they told The Register, and the download was removed from Microsoft’s website. There are now copies of the StagingTool executable floating around the internet, as one would expect, though we wouldn’t trust them.
StagingTool is a command-line application to list Windows functionality, enable/disable test features, and collect system telemetry. Armed with StagingTool, Windows Insiders can switch on stuff as they wish, and generally tinker with features that Microsoft is still developing.
For Windows bug hunters and ultra-early adopters, StagingTool may seem familiar. The internal application does much of the same things as third-party apps like ViVeTool, which were developed “for power users” who want to dig into the latest Windows features without waiting for a release – or for Microsoft to sneak out its own tool.
As to the differences between StagingTool and ViVeTool, aside from using Microsoft’s official method of toggling Windows features on and off versus methods discovered by third-party developers, XenoPanther told us there are several.
“For the most part they do the same job,” XenoPanther said, but noted that StagingTool has flags for offline images, the ability to conduct real-time tracing for individual features, and includes links to mission control for features that show up when queried.
“ViVeTool lacks those three features,” XenoPanther told us, “but ViVe has the ability to export/import IDs that are currently enabled on the system.”
Microsoft is well aware that third-party apps like ViVeTool exist. “Some of our more technical Insiders have discovered that some features are intentionally disabled in the builds we have flighted,” Windows Insider program director Amanda Langowski said in a blog post early last year.
“This is by design, and in those cases, we will only communicate about features that we are purposefully enabling for Insiders to try out and give feedback on.”
Microsoft didn’t immediately respond to our questions about the leak of the tool.
For those that want to try downloading a copy of StagingTool for themselves, XenoPanther said the SHA1 hash for the original executable is b1066e5aac4d4e39534d76a5636564f9b3f3c1f6 if you want to check that you have an original copy. Use at your own risk. And don’t forget: you can probably already do most of what you’d want to try with ViVeTool and similar third-party apps. ®
Source: Microsoft U-turns on internal Windows 11 testing tool • The Register
The Department for Science, Innovation and Technology has published a new report that investigates the level of cyber security skills in the UK, including the public sector.
In the Cyber security skills in the UK labour market 2023 report, which was researched by Ipsos, it was discovered that there is a significant skills gap across the public sector. One of the causes of this is the tight budgets that many organisations are under.
One contributor to the research spoke about the impact that funding is having, and is quoted in the document as saying:
“At the moment, we’re not getting funding streams through to do what we’re doing… Budgetary constraints are incredibly ferocious at the moment. Cybersecurity is a 24/7 problem. And we’re not paid to do that. So, everything’s been done on kind of grace and favour and best endeavours outside of hours.”
Alongside funding limitations holding back the cyber security of public sector organisations, there are also struggles around defining career pathways into public sector cyber security. The research suggested that this could be down to a lack of available roles, but it did also suggest that funding could be a contributing factor.
Another contributor, working for a public sector organisation with 1,000 or more employees, told the report:
“There are currently no defined career pathways. The council won’t contribute to the costs. We currently are offering no career pathways in cyber roles and cannot offer any apprenticeships. You are expected to have the knowledge or experience already and, if a role becomes available, then to apply for this role.”
Touching on the level of the skills gap that has opened up across the sector, the report stated that 30% of public bodies have an advanced skills gap, which is less than other sectors, however there is still concern about the capability of staff to keep systems secure. The research outlined how there is more scepticism surrounding staff using sufficiently strong passwords than in businesses, whilst 19% of respondents were also not confident in their organisation’s ability to write an incident response plan.
With the emphasis that is being placed on improving cyber security across the public sector, it would be believed that issues can be addressed before the gap widens. Seemingly, this could be rectified through increased funding and a more defined pathway for those wishing to embark on careers in public sector cyber security. More scope for apprenticeships, and a willingness to develop skills could see the gap close, especially with the noted increase in demand for cyber security professionals.
Source: Report outlines causes of cyber security skills gap | Public Sector News (publicsectorexecutive.com)
In our last article we introduced the cloud and explored some of the myths that business owners have had about cloud computing. Much of the apprehension around it is misplaced, but we also stressed that choosing a dedicated provider that offers genuine post-sale support is important, as not all providers are serving equally, even if they offer the same service.
In this piece we clear up some of the jargon that professionals use when they are referring to the cloud. After reading this, you will be savvy with cloud language, enabling you to navigate cloud solutions and to understand the value they can offer to your business.
Your applications are running on an underlying infrastructure that stores, computes and allocates resources to them, whether it is on-premises, cloud-based, or a mixture of the two.
Infrastructure-as-a-Service is a type of cloud computing framework which provides computer resources over the internet. Upon contracting an IaaS provider, they will supply and manage the infrastructure where your software will be hosted on a subscription basis; enabling a scalable, flexible and precise infrastructure solution for your apps.
Infrastructure as a service is a complex service. Depending on your technical literacy, it is often best to involve a team of IT professionals to help you to plan, implement and maintain the infrastructure so that it runs like clockwork for your business. With expert help, you can smoothly leverage cloud infrastructure to deliver enhanced value and scale securely.
Software as a Service delivers software services and data over an internet connection and web browser. Your provider will take full management and responsibility of both the security and back-up of your data, all within your agreed price.
SaaS is certainly the most popular choice of Cloud service – some of the most popular SaaS offerings include Microsoft 365, Google Workspace, and Xero Accounting amongst thousands of others. These services are also becoming more integrable, enabling more customised and streamlined workflows for businesses.
SaaS takes the stress and arduous process of managing your software and hardware out of your hands, leaving it in the capable hands of your provider’s expert team. For non-technical business leaders seeking to leverage technology and gain a competitive edge, SaaS is something of a godsend, as it takes the complexity out of managing and maintaining software away from the service user.
A Cloud Application is a software that you can access from any device that is connected to the internet, instead of installing it on each computer individually.
Compared to saving data on a physical hard drive on your computer, cloud storage is when you save your data to the cloud, where it is stored on remote servers and can be accessed directly from there. This essentially means that you store the data physically elsewhere in a secure data warehouse, but you no longer need to manage the physical infrastructure (I.e. on-premises servers) for doing so.
This takes us back to the point we made at the start of our first article, remote working is made possible with the cloud and cloud storage. Both your office and remote teams have seamless access to all the data that they need to fulfil their roles more efficiently and seamlessly.
This is the process of creating a virtual representation, or virtual replica, of a physical resource, such as a server, storage device, or network. These are called virtual machines.
Virtual machines behave like the physical resources they are based on; except they can now run multiple operating systems and applications at once. Imagine a computer being able to be broken down into mini virtual versions of itself and being able to operate across multiple physical computers (or in this case, servers) at once. This unlocks a great deal of flexibility and scalability for businesses, as virtualisation enables the consolidation and optimisation of hardware resources via cloud infrastructure.
For the final part of this article, we’ll highlight some of the benefits of using cloud technology in your business.
The cloud enables the ability for businesses to work flexibly with remote working capabilities. This ability allows teams to work together across different distances and times coherently and seamlessly. The cloud has unlocked the ability for businesses to tap into talent across the globe and to form teams from a range of geographic locations.
Operationally, teams can work on documents in real time, see version histories, including who is responsible for changes, as well as easily communicate via calls, video chats and messaging functionality. For developers and a business’s application infrastructure, the cloud liberates more scalable capacity for developing, deploying and hosting apps.
In all, the cloud achieves the kind of collaboration that can be found in the office, with some additional benefits too such as the potential for enhanced focus. This said, the cloud is not a granted collaboration paradise; it also takes an organised and responsible approach to get the best from cloud collaboration technology.
As much as we try to avoid them, disasters do happen, and they can be business defining. You need to have an efficient way of accessing all of your vital business data rapidly should the worst happen, and the cloud offers exactly that. The cloud allows you to continue with business-as-usual even in unusual circumstances. If a business experiences a disaster or emergency, such as a gas leak, flood, or fire for instance, they would be able to continue working from other locations with an internet connection, access the cloud, and resume operations.
A chief benefit to cloud computing is how flexible and scalable cloud solutions are, which often offer greater cost-efficiency as well. Whether a business is hosting its applications or servers in the cloud, or leverages SaaS solutions in its workflows, or uses VoIP technology, these can all be scaled easily and seamlessly to meet demand as the business scales up or down.
Compared to traditional forms of IT, the initial capital investment into cloud computing is far lower than it was in the past. Businesses using cloud solutions get much closer to paying only for what they are using, as cloud resources are scalable, precise and flexible in their nature. For businesses seeking to get more value at a relatively lower cost, cloud technology is a great leverage point to invest in.
4TC can support you with all the services you need to run your business effectively, from email and domain hosting to fully managing your whole IT infrastructure.
Setting up a great IT infrastructure is just the first step. Keeping it up to date, safe and performing at its peak requires consistent attention.
We can act as either your IT department or to supplement an existing IT department. We pride ourselves in developing long term relationships that add value to your business with high quality managed support, expert strategic advice, and professional project management.
Tech is transforming the planet at an increasingly swift rate, allowing teams around the world to achieve degrees of collaboration, communication, and productivity that were hard to imagine even as little as ten years ago. In the wake of the Covid-19 pandemic, many businesses turned towards cloud technology to enable them to work from home, using solutions such as Microsoft 365.
The Cloud is the element that makes remote working possible. When businesses consider adopting cloud technologies, they are aware of the potential benefits but can be daunted by the uncertainty or lack of knowledge about how it works and therefore how it could impact their business.
In the first of two articles, we will walk you through cloud computing and the myths that surround its use that often discourage its adoption. In our next piece, we will simplify some of the key technical jargon that professionals use when referring to it, and elucidate the benefits that businesses can reap from their cloud technology, enabling you to understand cloud computing and how it can be implemented to benefit your business.
Cloud computing is a series of platforms, services and infrastructure that enable digital services to be delivered via the internet, via data centres that host and process their information securely. A key potential of cloud computing is that it allows businesses to outsource IT functions, such as server capacity, to other providers without losing easy access to the data and services it’s hosting.
In the past, businesses had to manage their IT resources as a solo enterprise, where they would purchase, support and manage their own IT hardware and software platforms on their premises. This could lead to downtimes, inefficiencies and an oftentimes complicated and fragmented IT infrastructure that disempowered businesses from streamlining and optimising their workflows and systems to create more value and growth. This could be an expensive, frustrating and time-consuming set up to operate from, but with the cloud, many of these problems are surmountable.
By outsourcing servers and data storage to an outside provider specialising in offering this service, businesses save time and money on acquiring and maintaining hardware and pay for what they are using with the cloud server provider and scale it rapidly. In terms of applications, these can also be migrated securely to the cloud, and many software services are now offered via the cloud as Software as a Service (SaaS). With an internet connection, businesses can increasingly plug-in and play to the cloud to deliver their services, whilst outsourcing technical complexities in a highly cost-efficient way.
So what myths about the cloud are discouraging its adoption by those who could benefit from it?
“Value isn’t guaranteed when using Cloud Computing, so why would I bother?”
This myth could be true, insofar as the options and benefits have been examined in detail and have been left wanting.
There are many providers out there that will helpfully get you onboard and be supportive in that process, who then lose interest when it comes to providing genuine ongoing support into the future. This is wrong, it is unfair to sell a solution to someone who cannot see its full-value potential, so the provider should make it clear where that potential for value is, how it can be realised, and give an estimate of the scope of quantifiable benefits on offer.
A widely embraced cloud-based solution that offers clear value to many organisations, is the Microsoft 365 platform. It offers a range of familiar tools to businesses, with extended features such as live document collaboration, intelligent AI suggestions that speed up and enhance task completion, and an integrated interface that enables seamless switching between different tasks.
The saved time, improved quality of work and collaboration, and smart-searching features, alongside its flexible and fast scalability, offers a clear enough case for many businesses to adopt it. The principle is clear though, your IT partner should take their time to give a tailored assessment for your organisation, outline the benefits clearly, answer your questions, and then make a smooth implementation plan and provide onboarding and ongoing support. With this process, deriving profitable value from the cloud is assured.
“Is it important to back-up my data if we work in the Cloud?”
Yes, but with the caveat that regardless of your technology solution, having backups and contingencies is important. In the cloud’s case, creating and accessing backups is made much easier, though we would stress having multiple regular backups elsewhere offers the only assured backup solution. Overall though, storing, backing up and recovering data is typically easier with cloud services providers.
Cloud computing providers tend to provide protective measures as standard, such as robust data encryption and real time updating documents with recoverable version histories. There is not a particular reason to fear for your backups on the cloud, but it’s important to take fail-proof backup measures regardless of the platforms you are using to store your data.
“My data is missing, and I don’t know where it has gone”
It is very important to know where your data is being stored and thus to have control and oversight of it, as there can be legal, reputational and financial consequences to not protecting your data.
Cloud hosting providers are well aware of this crucial requirement and are also subject to it themselves. Alongside providers implementing measures to keep their cloud platforms secure, you can ask also them where they are storing your data if you are in doubt or can’t seem to find it, and they should be able to find it for you.
But, as we said earlier, not all Cloud providers are as they seem. Some aren’t interested in the value they can offer to you; they want your money and don’t care about your success. So it is important to ask about ongoing maintenance and support with potential providers, and to ensure these needs are enshrined in a contract to ensure peace of mind.
Therefore, it is essential that you read your contract carefully, as some have clauses that allow your provider to scan your data and carry out all sorts of other actions, so it is best to be careful rather than sorry.
4TC can support you with all the services you need to run your business effectively, from email and domain hosting to fully managing your whole IT infrastructure.
Setting up a great IT infrastructure is just the first step. Keeping it up to date, safe and performing at its peak requires consistent attention.
We can act as either your IT department or to supplement an existing IT department. We pride ourselves in developing long term relationships that add value to your business with high quality managed support, expert strategic advice, and professional project management.
You’ve all seen it. The media is awash with articles and commentary about how AI is going to take all of our jobs and leave only a small fraction of the population with hope of remaining in the careers they know and enjoy.
More research emerged recently which predicts that advertising agencies will replace 7.5% of existing jobs with AI by 2030, but it made a particularly interesting distinction: creative problem-solving roles will thrive.
This brings me on to something that’s been present in my mind for some time now, which is that there’s currently a race to the bottom in agency land. It’s a tough economic climate in general at the moment and, in pursuit of cutting costs, many bosses are exploring automating human roles – focusing on the immediate cost savings – without regard for possible future ramifications.
In particular, those naïvely believing they can lay off their team of copywriters and produce adequate work using ChatGPT are in for a nasty surprise. Of course, businesses should be thinking about how they can utilise emerging technologies, but let’s not get carried away.
It is not a creative replacement.
Another important thing to consider is that while generative artificial intelligence is likely to affect clerical, process-oriented roles, its rise will also pave the way for other opportunities which don’t yet exist. By educating ourselves on the topic and understanding not just where its strengths lie, but its limitations too, we can put ourselves in a strong position as more advancements are made.
Using what we do at WOAW for example — as a personal branding agency it would be impossible to deliver the level of personalisation in our client work as we do, without human control. The intricacies of the tone of voice, emotional understanding and the nuances that make each individual different are only fully understood and effectively applied by people.
That said, we’re thinking about where we can use AI, and it’s proven extremely effective in some key areas. Gathering basic information quickly, organising chronologically, building on existing ideas/concepts and making quick tweaks to things like the length of copy have all been great examples of its effectiveness.
It’s worth adding that even if you aren’t working in a role that’s considered ‘creative’, you aren’t necessarily doomed, either. Around 5 years ago, an AI researcher claimed that “We should stop training radiologists, because in 5 years, AI will have replaced the need for them.” Current demands for radiologists are off the charts and we can’t find enough of them. So, the overall point remains:
Yes, progress is moving very rapidly, but it’s the development of a tool; not a march towards extinction.
Source: AI scaremongering is rife, but creatives should fear not – Business Leader News

Email: support@4tc.co.uk
Tel: 020 7250 3840
5th Floor, 167‑169 Great Portland Street
London
W1W 5PF
Thremhall Park
Start Hill
Bishops Stortford
CM22 7WE

