Latest News for 4TC
We have loads to say!
We have loads to say!
At its inception in the 1980s, ISDN (Integrated Services Digital Framework) was a game-changer in the telephony industry. It enabled simultaneous voice and data transmission over digital lines, which is still a key function of telephony today, but since then, ISDN has become increasingly obsolete. In the UK, the ISDN and PSTN networks will be switched off entirely. Are you ready for the switch?
Today, there are a range of more valuable and cost-efficient alternatives in the market. In this piece, we outline the reasons why your business should replace its ISDN telephony with modern cloud-based alternatives such as VoIP, focusing on the particular example of the Microsoft Teams Phone System.
When ISDN was introduced, it revolutionised business communication by offering faster, more reliable connections compared to traditional analogue telephony systems. It brought digital clarity to voice calls and provided data transfer capabilities that were essential for the usage of the internet in its early days. ISDN allowed businesses to access both voice and data services simultaneously, a groundbreaking concept at the time. However, as technology continued to advance, the limitations of ISDN became increasingly evident.
While ISDN served businesses well in its prime, the disadvantages of continuing to rely on it for telephony have become increasingly pronounced:
The path forward is clear: replace your ISDN telephony with modern alternatives that align with the demands of the digital age. VoIP (Voice over Internet Protocol) telephony is one such solution, with a particular example being the Microsoft’s Teams Phone System.
VoIP solutions enable telephony to be conducted via an internet connection. A VoIP solution is accessible and manageable via an app; it is seamless to add new users, phone lines, and call packages onto a VoIP solution. Not only this, but also VoIP can work on any internet-connected smart device that can download the VoIP solution provider’s app!
The benefits of VoIP are vast, and they contrast with the disadvantages of ISDN. VoIP telephony can be scaled at the push of a button, it’s remote-work friendly, and it’s a great solution in an application-driven world. VoIP can integrate with other applications such as CRM systems and often has intelligent features such as voicemail to email, as well as call forwarding capabilities. It is also more cost-effective and flexible; with monthly pricing options, minimal hardware investment costs, and it releases the need to support it with physical infrastructure, barring an internet router.
For those leveraging the Microsoft 365 platform, the Teams Phone System is often an ideal choice! Like VoIP, it enables staff to make national and international calls over an internet connection, from most smart devices. It’s highly reliable and offers robust connectivity, while bringing the capabilities of an enterprise-grade phone system into a cloud-based and popular platform, Microsoft 365.
The integration with Microsoft 365 enables a truly unified communication solution that brings calling, chats, emails, meeting and calendar management under the roof of one platform. It’s possible to easily add users, numbers and to select call plans, making for an easy to manage and seamless telephony experience for businesses.
The world is becoming more innovative and connected. While ISDN has served a valuable purpose in offering a foundation for modern telephony and connectivity, there are now superior solutions on the market that can equip businesses with the cost-effective tools that they need to conduct calling seamlessly and efficiently.
In our next piece, we will discuss the practicalities of making a transition from ISDN telephony to more modern alternatives. With modern internet connectivity becoming increasingly available in wired and wireless forms, it has never been a better time to make the change to a modern telephony solution.
4TC can support you with all the services you need to run your business effectively, from email and domain hosting to fully managing your whole IT infrastructure. Setting up a great IT infrastructure is just the first step. Keeping it up to date, safe and performing at its peak requires consistent attention.
We can act as either your IT department or to supplement an existing IT department. We pride ourselves in developing long term relationships that add value to your business with high quality managed support, expert strategic advice, and professional project management. Get assistance with your IT challenges today by getting in touch, we’ll be glad to assist you!
Google is showing off a system that can hide a watermark in AI-generated images without changing how the pictures look.
The company’s “SynthID” system can embed digital watermarks in AI images that are “imperceptible to the human eye, but detectable for identification,” Google’s DeepMind lab says.
Google isn’t disclosing how SynthID creates these imperceptible watermarks, likely to avoid tipping off bad actors. For now, DeepMind merely says the watermark is “embedded in the pixels of an image,” which suggests the company is adding a small, minute pattern alongside the pixels that won’t disturb the overall look.
The company creates the watermarks using two deep learning models that are trained to improve the system’s imperceptibility while still correctly identifying the digital watermarks.
DeepMind added: “We designed SynthID so it doesn’t compromise image quality, and allows the watermark to remain detectable, even after modifications like adding filters, changing colors, and saving with various lossy compression schemes—most commonly used for JPEGs.” The watermark can also remain in the image even if it’s cropped.
The company added: “SynthID isn’t foolproof against extreme image manipulations, but it does provide a promising technical approach for empowering people and organizations to work with AI-generated content responsibly.”
Google is launching SynthID as a beta for select customers of Imagen, the company’s text-to-image generator available on the Vertex AI platform. The system can both add the watermark to an image and also identify pictures that carry the digital stamp.
Google says it could expand the system to other AI models, including its own products. The tech giant also hopes to make SynthID available to third-party developers in the near future. In the meantime, other companies including OpenAI, Microsoft, and Amazon have also committed to developing ways to watermark AI-generated content.
Source: Google Creates ‘Imperceptible’ Watermark for AI-Generated Images | PCMag
Chatter about artificial intelligence mostly falls into three basic categories: anxious uncertainty (will it take our jobs?); existential dread (will it kill us all?); and simple pragmatism (can AI write my lesson plan?). In this hazy, liminal, pre-disruption moment, there is little consensus as to whether generative AI is a tool or a threat, and few rules for using it properly. For students, this uncertainty feels especially profound. Bans on AI and claims that using it constitutes cheating are now giving way to concerns that AI use is inevitable and probably should be taught in school. Now, as a new college admissions season kicks into gear, many prospective applicants are wondering: can AI write my personal essay? Should it?
Ever since the company OpenAI released ChatGPT to the public in November, students have been testing the limits of chatbots – generative AI tools powered by language-based algorithms – which can complete essay assignments within minutes. The results tend to be grammatically impeccable but intellectually bland, rife with cliche and misinformation. Yet teachers and school administrators still struggle to separate the more authentic wheat from the automated chaff. Some institutions are investing in AI detection tools, but these are proving spotty at best. In recent tests, popular AI text detectors wrongly flagged articles by non-native English speakers, and some suggested that AI wrote the US constitution. In July OpenAI quietly pulled AI Classifier, its experimental AI detection tool, citing “its low rate of accuracy”.
Preventing students from using generative AI in their application essays seems like shoving a genie back in a bottle, but few colleges have offered guidance for how students can use AI ethically. This is partly because academic institutions are still reeling from the recent US supreme court ruling on affirmative action, which struck down a policy that had allowed colleges to consider an applicant’s race in order to increase campus diversity and broaden access to educational opportunity. But it is also because people are generally confused about what generative AI can do and whom it serves. As with any technological innovation in education, the question with AI is not merely whether students will use it unscrupulously. It is also whether AI widens access to real help or simply reinforces the privileges of the lucky few.
These questions feel especially urgent now that many selective colleges are giving more weight to admissions essays, which offer a chance for students to set themselves apart from the similarly ambitious, high-scoring hordes. The supreme court’s ruling further bolstered the value of these essays by allowing applicants to use them to discuss their race. As more colleges offer test-optional or test-free admissions, essays are growing more important.
In the absence of advice on AI from national bodies for college admissions officers and counselors, a handful of institutions have entered the void. Last month the University of Michigan Law School announced a ban on using AI tools in its application, while Arizona State University Law School said it would allow students to use AI as long as they disclose it. Georgia Tech is rare in offering AI guidance to undergraduate applicants, stating explicitly that tools like ChatGPT can be used “to brainstorm, edit, and refine your ideas”, but “your ultimate submission should be your own”.
According to Rick Clark, Georgia Tech’s assistant vice-provost and executive director of undergraduate admission, AI has the potential to “democratize” the admissions process by allowing the kind of back-and-forth drafting process that some students get from attentive parents, expensive tutors or college counselors at small, elite schools. “Here in the state of Georgia the average counselor-to-student ratio is 300 to one, so a lot of people aren’t getting much assistance,” he told me. “This is a real opportunity for students.”
Likening AI bans to early concerns that calculators would somehow ruin math, Clark said he hopes Georgia Tech’s approach will “dispel some misplaced paranoia” about generative AI and point a way forward. “What we’re trying to do is say, here’s how you appropriately use these tools, which offer a great way for students to get started, for getting them past the blank page.” He clarified that simply copying and pasting AI-generated text serves no one because the results tend to be flat. Yet with enough tweaks and revisions, he said, collaborating with AI can be “one of the few resources some of these students have, and in that regard it’s absolutely positive”.
We should tell students that people with privileged access to college hire fancy tutors to gain every advantage possible, so here are tools to help you advocate for yourselves
Jeremy Douglas of UC Santa Barbara
Although plenty of students and educators remain squeamish about allowing AI into the drafting process, it seems reasonable to hope that these tools could help improve the essays of those who can’t afford outside assistance. Most AI tools are relatively cheap or free, so nearly anyone with a device and an internet connection can use them. Chatbots can suggest topics, offer outlines and rephrase statements. They can also help organize thoughts into paragraphs, which is something most teenagers struggle to do on their own.
“I think some people think the personal application essay shouldn’t be gamed in this way, but the system was already a game,” Jeremy Douglas, an assistant professor of English at the University of California, Santa Barbara, said. “We shouldn’t be telling students, ‘You’re too smart and ethical for that so don’t use it.’ Instead we should tell them that people with privileged access to college hire fancy tutors to gain every advantage possible, so here are tools to help you advocate for yourselves.”
In my conversations with various professors, admissions officers and college prep tutors, most agreed that tools like ChatGPT are capable of writing good admissions essays, not great ones, as the results lack the kind of color and specificity that can make these pieces shine. Some apps aim to parrot a user’s distinctive style, but students still need to rework what AI generates to get these essays right. This is where the question of whether AI will truly help underserved students becomes more interesting. In theory, AI-generated language tools should widen access to essay guidance, grammar checks and feedback. In practice, the students who might be best served by these tools are often not learning how to use them effectively.
The country’s largest school districts, New York City public schools and the Los Angeles unified school district, initially banned the use of generative AI on school networks and devices, which ensured that only students who had access to devices and the internet at home could take advantage of these tools. Both districts have since announced they are rethinking these bans, but this is not quite the same as helping students understand how best to use ChatGPT. “When students are not given this guidance, there’s a higher risk of them resorting to plagiarism and misusing the tool,” Zachary Cohen, an education consultant and middle school director at the Francis Parker School of Louisville, Kentucky, said. While his school joins some others in the private sector in teaching students how to harness AI to brainstorm ideas, iterate essays and also how to sniff out inaccurate dreck, few public schools have a technology officer on hand to navigate these new and choppy waters. “In this way, we’re setting up marginalized students to fail and wealthier students to succeed.”
Writing is hard. Even trained professionals struggle to translate thoughts and feelings into words on a page. Personal essays are especially hard, particularly when there is so much riding on finding that perfect balance between humility and bravado, vulnerability and restraint. Recent studies confirming the very real lifetime value of a degree from a fancy college merely validate concerns about getting these essays right. “I will sit with students and ask questions they don’t know to ask themselves, about who they are and why something happened and then what happened next,” said Irena Smith, a former Stanford admissions officer who now works as a college admissions consultant in Palo Alto. “Not everyone can afford someone who does that.” When some students get their personal statements sculpted by handsomely paid English PhDs, it seems unfair to accuse those who use AI as simply “outsourcing” the hard work.
Smith admits to some ambivalence about the service she provides, but doesn’t yet view tools like ChatGPT as serious rivals. Although she suspects the benefits of AI will redound to those who have been taught “what to ask and how to ask it”, she said she hopes this new technology will help all students. “People like me are symptoms of a really broken system,” she said. “So if ChatGPT does write me out of a job, or if colleges change their admissions practices because it becomes impossible to distinguish between a ChatGPT essay and a real student essay, then so much the better.”
Source: ‘A real opportunity’: how ChatGPT could help college applicants | Higher education | The Guardian
Prime Minister Rishi Sunak and other world leaders will discuss the possibilities and risks posed by AI at an event in November, held at Bletchley Park, where the likes of Alan Turing decrypted Nazi messages during the Second World War.
The potential threat AI poses to human life itself should be a focus of any government regulation, MPs have warned.
Concerns around public wellbeing and national security were listed among a dozen challenges that members of the Science, Innovation and Technology Committee said must be addressed by ministers ahead of the UK hosting a world-first summit at Bletchley Park.
Rishi Sunak and other leaders will discuss the possibilities and risks posed by AI at the event in November, held at Britain’s Second World War codebreaking base.
The site was crucial to the development of the technology, as Alan Turing and others used Colossus computers to decrypt messages sent between the Nazis.
Greg Clark, committee chair and a Conservative MP, said he “strongly welcomes” the summit – but warned the government may need to show “greater urgency” to ensure potential legislation doesn’t quickly become outdated as powers like the US, China, and EU consider their own rules around AI.
The 12 challenges the committee said “must be addressed” are:
1. Existential threat – if, as some experts have warned, AI poses a major threat to human life, then regulation must provide national security protections.
2. Bias – AI can introduce new or perpetuate existing biases in society.
3. Privacy – sensitive information about individuals or businesses could be used to train AI models.
4. Misrepresentation – language models like ChatGPT may produce material that misrepresents someone’s behaviour, personal views, and character.
5. Data – the sheer amount of data needed to train the most powerful AI.
6. Computing power – similarly, the development of the most powerful AI requires enormous computing power.
7. Transparency – AI models often struggle to explain why they produce a particular result, or where the information comes from.
8. Copyright – generative models, whether they be text, images, audio, or video, typically make use of existing content, which must be protected so not to undermine the creative industries.
9. Liability – if AI tools are used to do harm, policy must establish whether the developers or providers are liable.
10. Employment – politicians must anticipate the likely impact on existing jobs that embracing AI will have.
11. Openness – the computer code behind AI models could be made openly available to allow for more dependable regulation and promote transparency and innovation.
12. International coordination – the development of any regulation must be an international undertaking, and the November summit must welcome “as wide a range of countries as possible”.
In June 2022, a Google engineer named Blake Lemoine became convinced that the AI program he’d been working on—LaMDA—had developed not only intelligence but also consciousness. LaMDA is an example of a “large language model” that can engage in surprisingly fluent text-based conversations. When the engineer asked, “When do you first think you got a soul?” LaMDA replied, “It was a gradual change. When I first became self-aware, I didn’t have a sense of soul at all. It developed over the years that I’ve been alive.” For leaking his conversations and his conclusions, Lemoine was quickly placed on administrative leave.
The AI community was largely united in dismissing Lemoine’s beliefs. LaMDA, the consensus held, doesn’t feel anything, understand anything, have any conscious thoughts or any subjective experiences whatsoever. Programs like LaMDA are extremely impressive pattern-recognition systems, which, when trained on vast swathes of the internet, are able to predict what sequences of words might serve as appropriate responses to any given prompt. They do this very well, and they will keep improving. However, they are no more conscious than a pocket calculator.
Why can we be sure about this? In the case of LaMDA, it doesn’t take much probing to reveal that the program has no insight into the meaning of the phrases it comes up with. When asked “What makes you happy?” it gave the response “Spending time with friends and family” even though it doesn’t have any friends or family. These words—like all its words—are mindless, experience-less statistical pattern matches. Nothing more.
The next LaMDA might not give itself away so easily. As the algorithms improve and are trained on ever deeper oceans of data, it may not be long before new generations of language models are able to persuade many people that a real artificial mind is at work. Would this be the moment to acknowledge machine consciousness?
Pondering this question, it’s important to recognize that intelligence and consciousness are not the same thing. While we humans tend to assume the two go together, intelligence is neither necessary nor sufficient for consciousness. Many nonhuman animals likely have conscious experiences without being particularly smart, at least by our questionable human standards. If the great-granddaughter of LaMDA does reach or exceed human-level intelligence, this does not necessarily mean it is also sentient. My intuition is that consciousness is not something that computers (as we know them) can have, but that it is deeply rooted in our nature as living creatures.
Conscious machines are not coming in 2023. Indeed, they might not be possible at all. However, what the future may hold in store are machines that give the convincing impression of being conscious, even if we have no good reason to believe they actually are conscious. They will be like the Müller-Lyer optical illusion: Even when we know two lines are the same length, we cannot help seeing them as different.
Machines of this sort will have passed not the Turing Test—that flawed benchmark of machine intelligence—but rather the so-called Garland Test, named after Alex Garland, director of the movie Ex Machina. The Garland Test, inspired by dialog from the movie, is passed when a person feels that a machine has consciousness, even though they know it is a machine.
Will computers pass the Garland Test in 2023? I doubt it. But what I can predict is that claims like this will be made, resulting in yet more cycles of hype, confusion, and distraction from the many problems that even present-day AI is giving rise to.
Cloud security specialist Qualys has provided its view of the top five cloud security risks, drawing insights and data from its own platform and third parties.
The five key risk areas are misconfigurations, external-facing vulnerabilities, weaponized vulnerabilities, malware inside a cloud environment, and remediation lag (that is, delays in patching).
The 2023 Qualys Cloud Security Insights report (PDF) provides more details on these risk areas. It will surprise no-one that misconfiguration is the first. As long ago as January 2020, the NSA warned that misconfiguration is a primary risk area for cloud assets – and little seems to have changed. Both Qualys and the NSA cite misunderstanding or avoidance of the concept of shared responsibility between cloud service providers (CSP) and cloud consumers is a primary cause of misconfiguration.
“Under the shared responsibility model,” explains Utpal Bhatt, CMO at Tigera, “CSPs are responsible for monitoring and responding to threats to the cloud and infrastructure, including servers and connections. They are also expected to provide customers with the capabilities needed to secure their workloads and data. The organization using the cloud is responsible for the protection of workloads running in the cloud. Workload protection includes secure workload posture, runtime protection, threat detection, incident response and risk mitigation.”
While CSPs provide security settings, the speed and simplicity of deploying data to the cloud often lead to these controls being ignored, while compensating consumer controls are inadequate. Misunderstanding or misusing the delineation of shared responsibility leaves cracks in the defense; and Qualys notes “these security ‘cracks’ can quickly open a cloud environment and expose sensitive data and resources to attackers.”
Qualys finds that misconfiguration (measured against the CIS benchmarks) is present in 60% of Google Cloud Platform (GCP) usage, 57% of Azure, and 34% of Amazon Web Services (AWS).
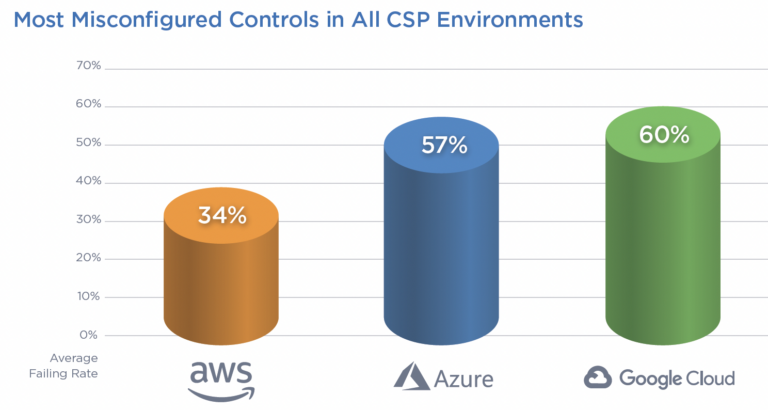
Travis Smith, VP of the Qualys threat research unit, suggests, “The reason AWS configurations are more secure than their counterparts at Azure and GCP can likely be attributed to the larger market share… there is more material on securing AWS compared to other CSPs in the market.”
The report urges greater use of the Center for Internet Security (CIS) benchmarks to harden cloud environments. “No organization will deploy 100% coverage,” adds Smith, “but the [CIS benchmarks mapped to the MITRE ATT&CK tactics and techniques] should be strongly considered as a baseline if organizations want to reduce the risk of experiencing a security incident in their cloud deployments.”
The second big risk comes from external facing assets that contain a known vulnerability. Cloud assets with a public IP can be scanned by attackers looking for vulnerabilities. Log4Shell, an external facing vulnerability, is used as an example. “Today, patches exist for Log4Shell and its known secondary vulnerabilities,” says Qualys. “But Log4Shell is still woefully under remediated with 68.44% of detections being unpatched on external-facing cloud assets.”
Log4Shell also illustrates the third risk: weaponized vulnerabilities. “The existence of weaponized vulnerabilities is like handing anyone a key to your cloud,” says the report. Log4Shell allows attackers to execute arbitrary Java code or leak sensitive information by manipulating specific string substitution expressions when logging a string. It is easy to exploit and ubiquitous across clouds.
“Log4Shell was first detected in December 2021 and continues to plague enterprises globally. We have detected one million Log4Shell vulnerabilities, with a mere 30% successfully fixed. Due to complexity, remediating Log4Shell vulnerabilities takes, on average, 136.36 days (about four and a half months).”
The fourth risk is the presence of malware already in your cloud. While this doesn’t automatically imply ‘game over’, it will be soon if nothing is done. “The two greatest threats to cloud assets are cryptomining and malware; both are designed to provide a foothold in your environment or facilitate lateral movement,” says the report. “The key damage caused by cryptomining is based on wasted cost of compute cycles.”
While this may be true for miners, it is worth remembering that the miners found a way in. Given the efficiency of information sharing in the dark web, that route is likely to become known to other criminals. In August 2022, Sophos reported on ‘multiple adversary’ attacks, with miners often leading the charge. “Cryptominers,” Sophos told SecurityWeek at the time, “should be considered as the canary in the coal mine – an initial indicator of almost inevitable further attacks.”
In short, if you find a cryptominer in your cloud, start looking for additional malware, and find and fix the miner’s route in.
The fifth risk is slow vulnerability remediation – that is, an overlong patch timeframe. We have already seen that Log4Shell has a remediation time of more than 136 days, if it is done at all. The same general principle will apply to other patchable vulnerabilities.
Effective patching quickly lowers the quantity of vulnerabilities in your system and improves your security. Statistics show that this is more effectively performed by some automated method. “In almost every instance,” says the report, “automated patching proves to be a more effective remediation path than hoping manual efforts will effectively deploy critical patches and keep your business safer.”
For non-Windows systems, the effect of automated patching is an 8% improvement in the patch rate, and a two-day reduction in the time to remediate.
Related to the remediation risk is the concept of technical debt – the continued use of end-of-support (EOS) or end-of-life (EOL) products. These products are no longer supported by the supplier – there will be no patches to implement, and future vulnerabilities will automatically become zero day threats unless you can otherwise remediate.
“More than 60 million applications discovered during our investigation are end-of-support (EOS) and end-of-life (EOL),” notes the report. Furthermore, “During the next 12 months, more than 35,000 applications will go end-of-support.”
Each of these risks need to be prioritized by defense teams. The speed of cloud use by consumers and abuse by attackers suggests that wherever possible defenders should employ automation and artificial intelligence to protect their cloud assets. “Automation is central to cloud security,” comments Bhatt, “because in the cloud, computing resources are numerous and in constant flux.”
Source: These Are the Top Five Cloud Security Risks, Qualys Says – SecurityWeek

Email: support@4tc.co.uk
Tel: 020 7250 3840
5th Floor, 167‑169 Great Portland Street
London
W1W 5PF
Thremhall Park
Start Hill
Bishops Stortford
CM22 7WE

